Docker & Kubernetes
Docker & Kubernetes
Dockerfile
Each language has a different Dockerfile. Choose the one matching your SDK language.
Python
TypeScript
Application entry point (Python)
Building and running
Docker Compose
Run with:
Kubernetes deployment
Kubernetes manifests are language-agnostic. The only difference is the Docker image referenced and any build steps. Use the appropriate Dockerfile from the section above to build your image, then deploy with the same manifests regardless of language.
Deployment manifest
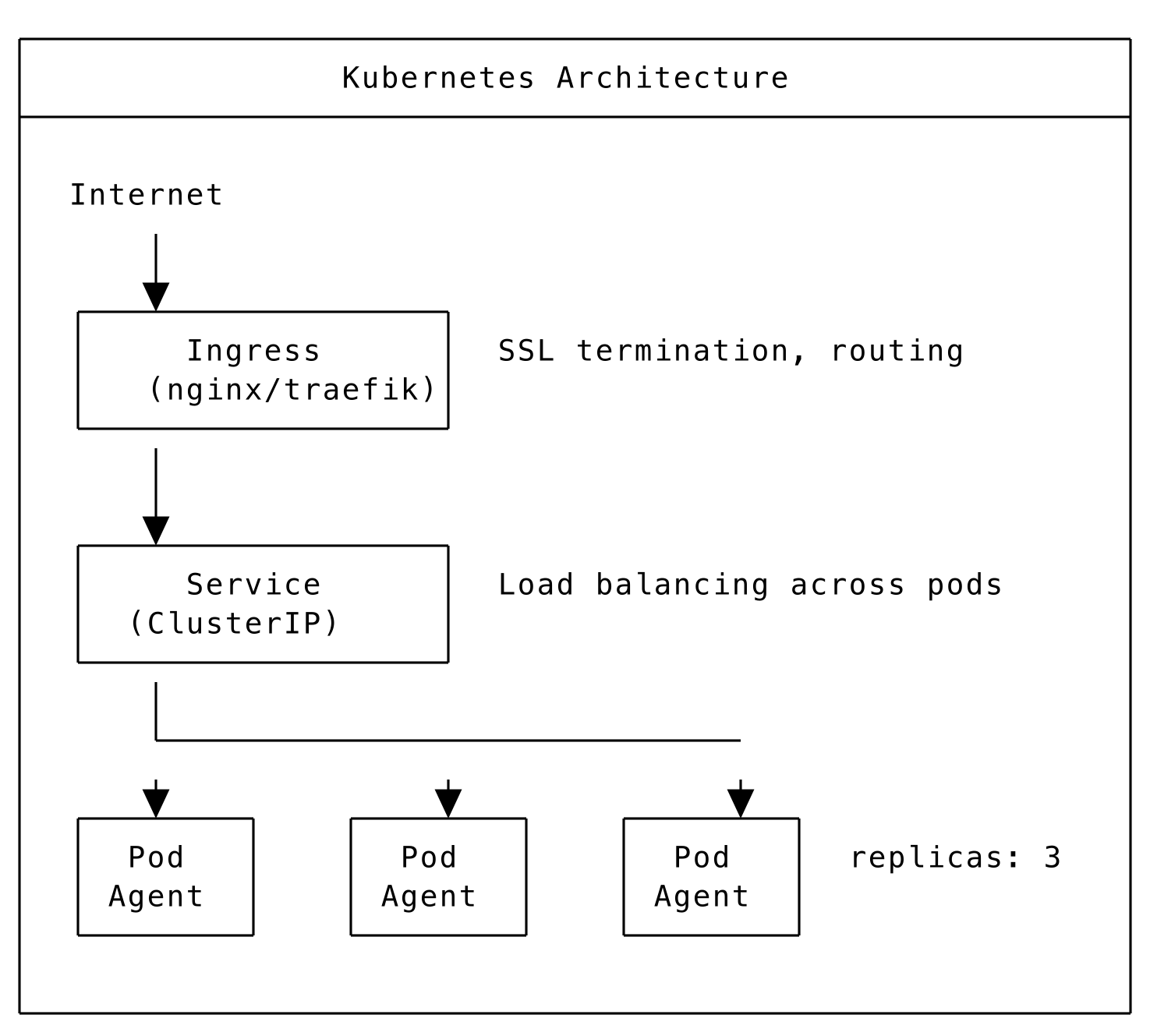
Service manifest
Ingress manifest
Secrets
Kubernetes architecture
Deploying to Kubernetes
Horizontal Pod Autoscaler
Multi-architecture builds
Build with:
Container best practices
Security
- Run as non-root user
- Use minimal base images (slim, alpine)
- Scan images for vulnerabilities
- Don’t store secrets in images
Performance
- Use multi-stage builds to reduce image size
- Layer dependencies efficiently
- Set appropriate resource limits
Reliability
- Add health checks
- Use restart policies
- Configure proper logging
- Set graceful shutdown handling