Production Deployment
Production checklist
Security
- HTTPS enabled with valid certificates
-
SWML_BASIC_AUTH_PASSWORDconfigured (username defaults tosignalwire) - Firewall rules in place
- No secrets in code or logs (SDK masks credentials in startup output automatically)
Reliability
- Process manager (systemd/supervisor)
- Health checks configured
- Logging to persistent storage
- Error monitoring/alerting
Performance
- Multiple workers for concurrency
- Reverse proxy (nginx) for SSL termination
- Load balancing if needed
Environment variables
Running in production
Production deployment differs significantly by language. Each SDK provides its own HTTP server or integrates with language-specific production servers.
Python
TypeScript
Use uvicorn with multiple workers:
Create an entry point module:
Systemd service
Create /etc/systemd/system/signalwire-agent.service. Adjust ExecStart for your language:
Enable and start:
Nginx reverse proxy
Enable the site:
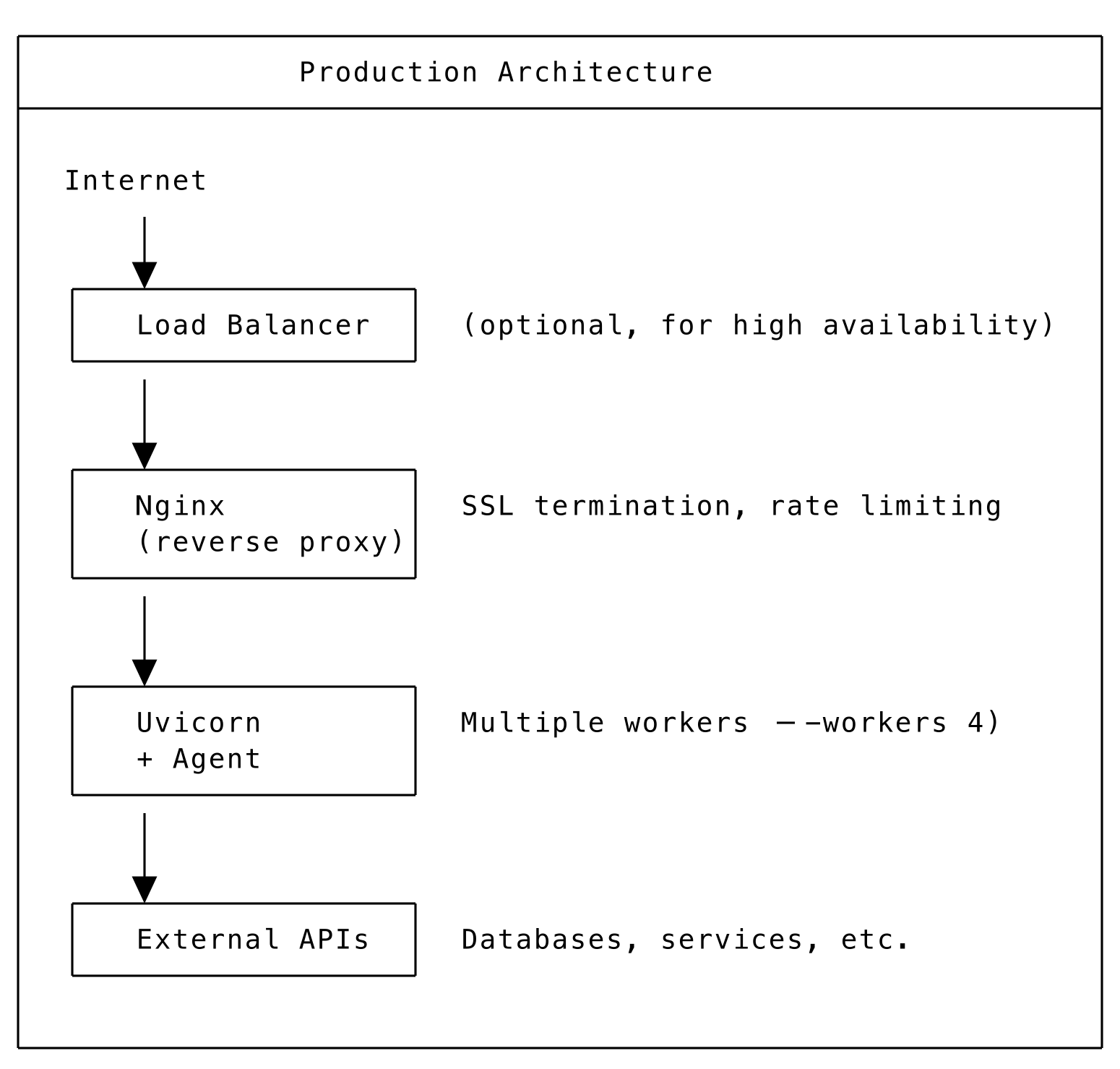
Production architecture
SSL configuration
Using environment variables
Let’s Encrypt with Certbot
Health checks
For AgentServer deployments:
Response:
For load balancers, use this endpoint to verify agent availability.
Logging configuration
Or use environment variable:
Monitoring
Prometheus metrics
Add custom metrics to your agent:
External monitoring
- Uptime monitoring: Monitor the health endpoint
- Log aggregation: Ship logs to ELK, Datadog, or similar
- APM: Use Application Performance Monitoring tools
Scaling considerations
Vertical scaling
| TypeScript | Increase PM2 instances (pm2 scale agent 8) |
- Use larger server instances
- Optimize agent code and external calls
Horizontal scaling
- Multiple server instances behind load balancer
- Stateless agent design
- Shared session storage (Redis) if needed
Serverless
- Auto-scaling with Lambda/Cloud Functions
- Pay per invocation
- No server management
Built-in security features
The SDK includes several security hardening features enabled by default.
Security headers
All HTTP responses automatically include security headers:
No configuration is needed — these headers are added automatically by middleware on AgentBase, AgentServer, and SWMLService.
SSRF protection
DataMap HTTP requests, skill remote URLs, and MCP gateway URLs are validated against private IP ranges to prevent Server-Side Request Forgery attacks. By default, requests to internal networks (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16, 127.0.0.0/8, 169.254.0.0/16, and IPv6 equivalents) are blocked.
To allow private URLs (e.g., when your backend services are on a private network):
Timing-safe authentication
Basic auth credential comparison uses hmac.compare_digest() to prevent timing side-channel attacks. SWAIG token validation also uses constant-time comparison.
Credential masking
Startup log output shows (credentials configured) instead of the actual password:
Default authentication username
SWML_BASIC_AUTH_USER defaults to signalwire when not explicitly set. You only need to configure SWML_BASIC_AUTH_PASSWORD:
Proxy header validation
X-Forwarded headers (X-Forwarded-Host, X-Forwarded-Proto) are only trusted when explicitly configured. Set SWML_TRUST_PROXY_HEADERS=true if your agent runs behind a reverse proxy and you want the SDK to auto-detect the public URL from forwarded headers:
When SWML_PROXY_URL_BASE is set via environment variable, proxy headers are automatically trusted for URL construction.
Security best practices
DO:
- Use HTTPS everywhere
- Set strong basic auth credentials
- Use environment variables for secrets
- Enable firewall and limit access
- Regularly update dependencies
- Monitor for suspicious activity
DON’T:
- Expose debug endpoints in production
- Log sensitive data
- Use default credentials
- Disable SSL verification
- Run as root user