Production
Production Deployment
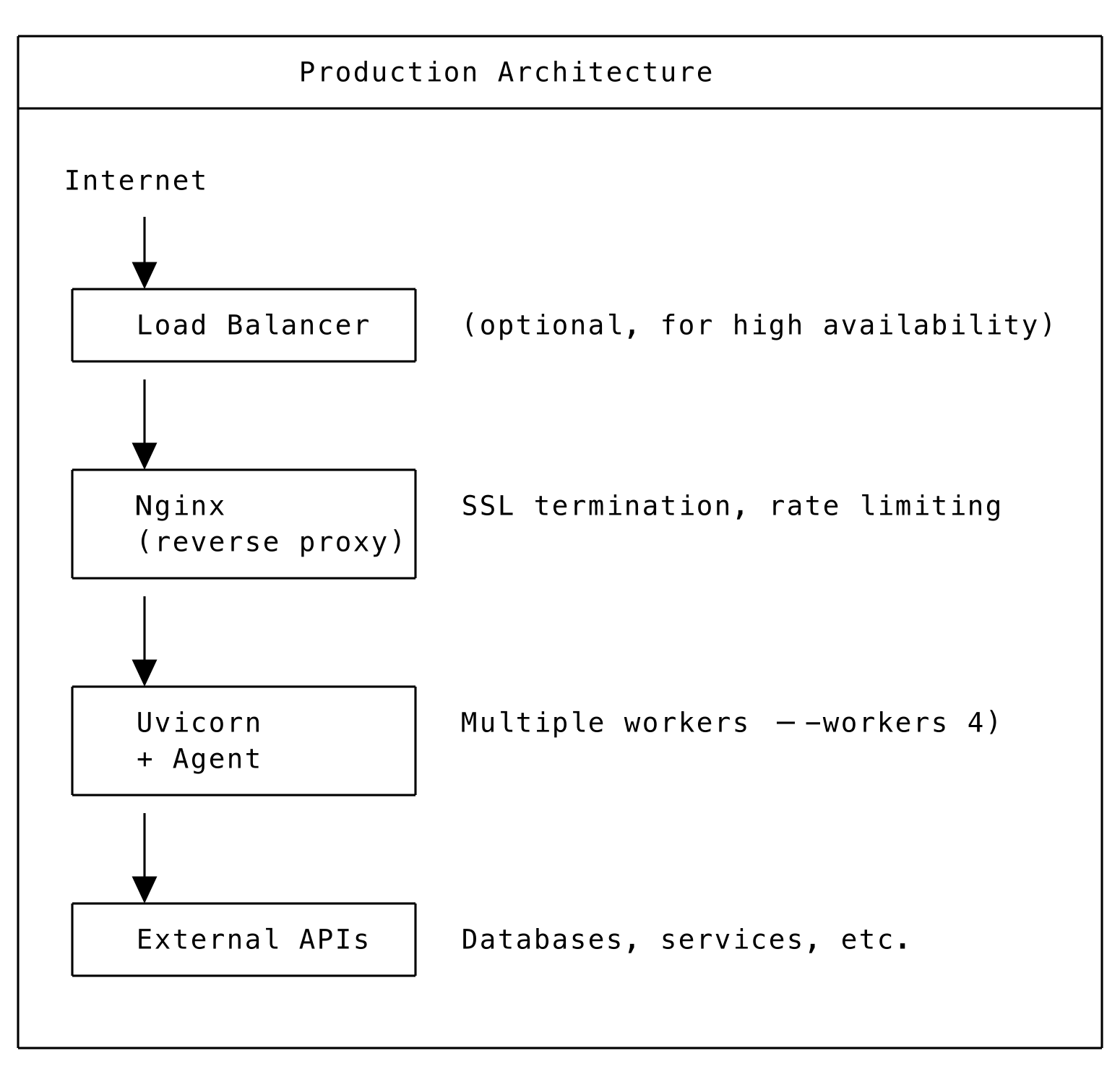
Deploy agents to production with proper SSL, authentication, monitoring, and scaling. Use uvicorn workers, nginx reverse proxy, and systemd for process management.
Production Checklist
Security
- HTTPS enabled with valid certificates
- Basic authentication configured
- Firewall rules in place
- No secrets in code or logs
Reliability
- Process manager (systemd/supervisor)
- Health checks configured
- Logging to persistent storage
- Error monitoring/alerting
Performance
- Multiple workers for concurrency
- Reverse proxy (nginx) for SSL termination
- Load balancing if needed
Environment Variables
Running with Uvicorn Workers
For production, run with multiple workers:
Create an entry point module:
Systemd Service
Create /etc/systemd/system/signalwire-agent.service:
Enable and start:
Nginx Reverse Proxy
Enable the site:
Production Architecture
SSL Configuration
Using Environment Variables
Let’s Encrypt with Certbot
Health Checks
For AgentServer deployments:
Response:
For load balancers, use this endpoint to verify agent availability.
Logging Configuration
Or use environment variable:
Monitoring
Prometheus Metrics
Add custom metrics to your agent:
External Monitoring
- Uptime monitoring: Monitor the health endpoint
- Log aggregation: Ship logs to ELK, Datadog, or similar
- APM: Use Application Performance Monitoring tools
Scaling Considerations
Vertical Scaling
- Increase uvicorn workers (
--workers N) - Use larger server instances
- Optimize agent code and external calls
Horizontal Scaling
- Multiple server instances behind load balancer
- Stateless agent design
- Shared session storage (Redis) if needed
Serverless
- Auto-scaling with Lambda/Cloud Functions
- Pay per invocation
- No server management
Security Best Practices
DO:
- Use HTTPS everywhere
- Set strong basic auth credentials
- Use environment variables for secrets
- Enable firewall and limit access
- Regularly update dependencies
- Monitor for suspicious activity
DON’T:
- Expose debug endpoints in production
- Log sensitive data
- Use default credentials
- Disable SSL verification
- Run as root user