Docker Kubernetes
Docker & Kubernetes
Containerize your agents with Docker and deploy to Kubernetes for scalable, manageable production deployments.
Dockerfile
requirements.txt
Application Entry Point
Building and Running
Docker Compose
Run with:
Kubernetes Deployment
Deployment Manifest
Service Manifest
Ingress Manifest
Secrets
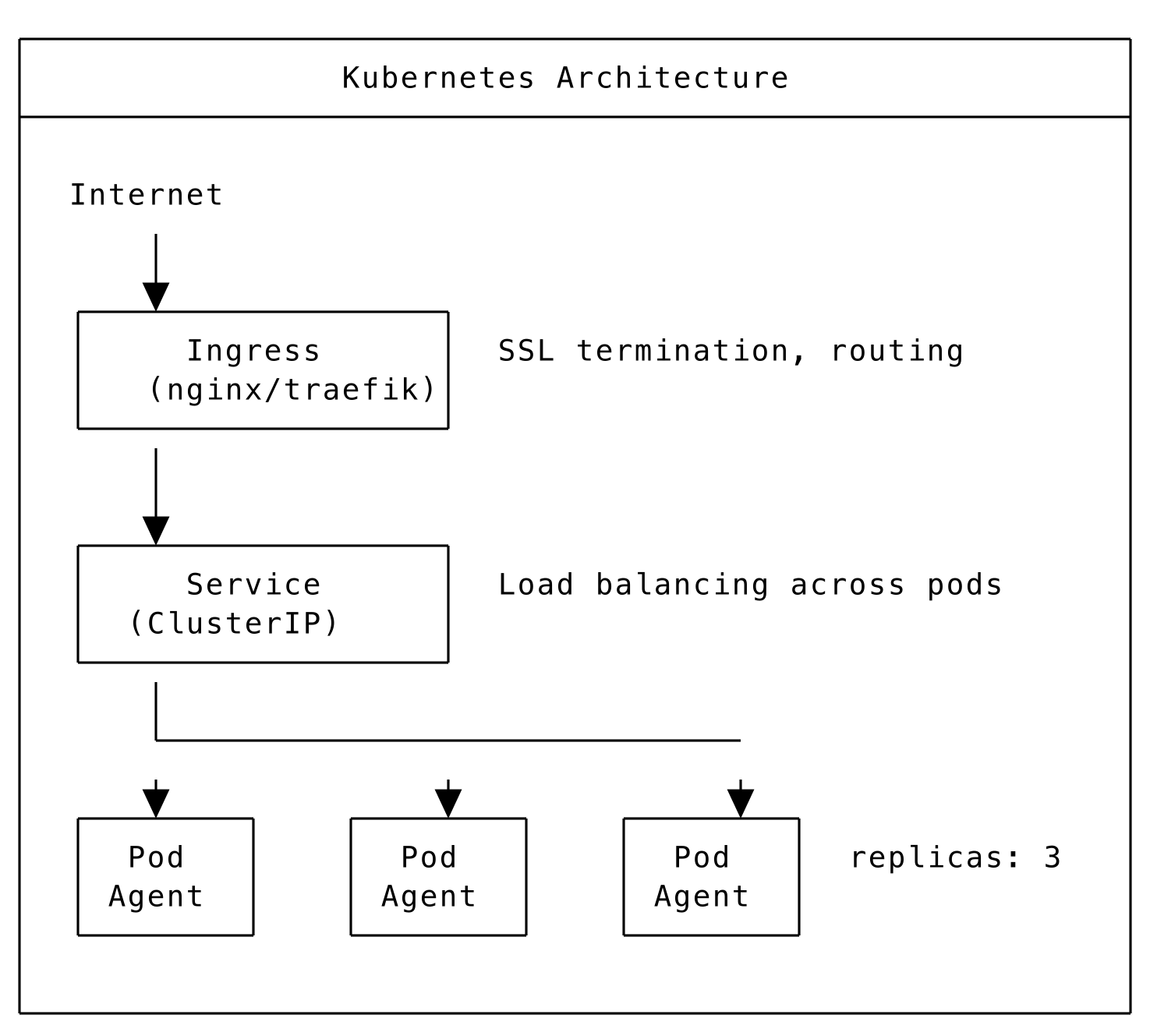
Kubernetes Architecture
Deploying to Kubernetes
Horizontal Pod Autoscaler
Multi-Architecture Builds
Build with:
Container Best Practices
Security
- Run as non-root user
- Use minimal base images (slim, alpine)
- Scan images for vulnerabilities
- Don’t store secrets in images
Performance
- Use multi-stage builds to reduce image size
- Layer dependencies efficiently
- Set appropriate resource limits
Reliability
- Add health checks
- Use restart policies
- Configure proper logging
- Set graceful shutdown handling